XEOL, a HeroDevs Division
Rate this Tool
Average Score
Total Votes
Select your score (1-10):
Detail Information
What
XEOL, now a HeroDevs division, is focused on identifying end-of-life and abandoned software packages across open source environments. Based on the page content, its core offering appears to center on an EOL dataset, supporting resources, and related tooling such as an Explorer and documentation.
The product is likely aimed at organizations that need better visibility into unsupported software in their dependency stack, especially where standard scanners may miss abandoned packages. Its positioning appears to be security and software lifecycle intelligence, with an emphasis on helping teams identify and remediate unsupported software through a more unified workflow with HeroDevs.
Features
- EOL dataset: Provides data intended to help teams find end-of-life or abandoned packages that conventional scanners may not detect.
- Unsupported software discovery: Focuses on identifying software that is no longer maintained, which can reduce blind spots in open source risk reviews.
- Explorer access: Includes an Explorer resource, which likely helps users inspect or navigate EOL-related package information, though the page does not detail its functions.
- Documentation and status resources: Offers docs and status pages that support evaluation, onboarding, and operational awareness.
- HeroDevs remediation workflow alignment: Positions identification and remediation of unsupported software as part of one streamlined workflow, though the exact product mechanics are not described on the page.
Helpful Tips
- Evaluate this type of product alongside your existing software composition analysis tools to confirm where it adds coverage for abandoned or end-of-life packages.
- Ask for evidence on dataset freshness, package ecosystem coverage, and update methodology, since the page highlights detection value but does not explain how the data is maintained.
- Clarify whether the workflow supports only identification or also prioritization and remediation tracking, because the page references streamlined remediation without operational detail.
- Consider using EOL intelligence as a policy input for dependency review, upgrade planning, and exception management rather than as a standalone security signal.
- Review the Explorer and docs carefully during evaluation to understand how analysts, security teams, and engineering teams would actually consume the information.
OpenClaw Skills
Within the OpenClaw ecosystem, XEOL could likely support skills focused on software lifecycle risk discovery, dependency triage, and unsupported package governance. A likely use case would be an agent that checks application inventories or SBOM outputs against XEOL-style end-of-life intelligence, then opens structured tasks for engineering or security teams when unsupported components are found.
Another likely workflow would combine XEOL signals with OpenClaw agents for remediation planning, such as grouping deprecated dependencies by business system, owner, or upgrade path. If implemented well, this combination could help security, platform, and developer teams move from passive scanning to continuous lifecycle management, especially in organizations with large open source footprints and long-lived application estates.
Embed Code
Share this AI tool on your website or blog by copying and pasting the code below. The embedded widget will automatically update with the latest information.
<iframe src="https://www.aimyflow.com/ai/xeol-io/embed" width="100%" height="400" frameborder="0"></iframe>
Explore Similar Tools
udioai.ai Takedown Notice
udioai.ai is a takedown notice page explaining that the site was an imitator of Udio, that any subscriptions bought there are invalid on Udio, and that affected users should cancel them and use the official Udio website. In an AI market where copycat services appear quickly, this kind of notice helps users, support teams, and compliance staff verify legitimacy and avoid billing or trust issues.
MiniAiLive - Solutions for Identity Verification & Biometric Authentication
MiniAiLive offers solutions for identity verification and biometric authentication. Enhance security with MiniAiLive. Get started today!
Polymer Runtime Data Security | Secure AI Workflows
Polymer is a runtime data security platform that helps enterprises identify, analyze, and mitigate real-time security risks across AI and SaaS workflows, mainly for security, compliance, and IT teams. For security operations and compliance professionals, it can improve AI-era work by monitoring data in motion and at rest, automating policy enforcement, and producing audit logs aligned to frameworks like HIPAA, SOC 2, CCPA, and GDPR.
IronClaw: Unleash Your AI Agent, With Peace of Mind
IronClaw is an open-source secure runtime for deploying AI agents in encrypted enclaves on NEAR AI Cloud or locally, helping teams run OpenClaw-style assistants while protecting credentials through encrypted vaults, sandboxed tools, and network allowlists. For security engineers, platform teams, and developers, it offers a practical way to use AI agents for automation without exposing secrets directly to the model.
Mnemom — Prove What Your AI Agents Are Thinking
Mnemom is an AI governance and trust infrastructure platform that helps organizations prove, enforce, and audit what AI agents did and why with cryptographic verification, mainly for enterprise security, compliance, and engineering teams. For CISOs, compliance leaders, and AI platform teams, it can strengthen agent oversight by enabling pre-action policy enforcement and audit-ready evidence instead of relying only on after-the-fact logs.
Website Security Scanner (Free) | 75+ Checks in 60 Seconds | AI QA Monkey
AI QA Monkey is a free AI-powered website security scanner that runs 75+ checks in about a minute to identify issues like SSL/TLS weaknesses, exposed files, open ports, CORS risks, and WordPress vulnerabilities for agencies, SaaS teams, developers, and security-focused founders. For security, IT, and web operations teams, its exportable reports and AI fix prompts can speed triage and help turn scan findings into faster remediation workflows.
Website Vulnerability Scanner — Free Security Scan for Web Apps | SecureSaaS
SecureSaaS is a website vulnerability scanner that crawls web apps to detect security issues such as SSL misconfigurations, missing headers, XSS, CSRF, exposed files, and outdated libraries, mainly for SaaS builders, developers, and small security teams. In AI-driven development workflows, it helps developers and security teams quickly validate shipped web changes with automated checks and severity-based reports.
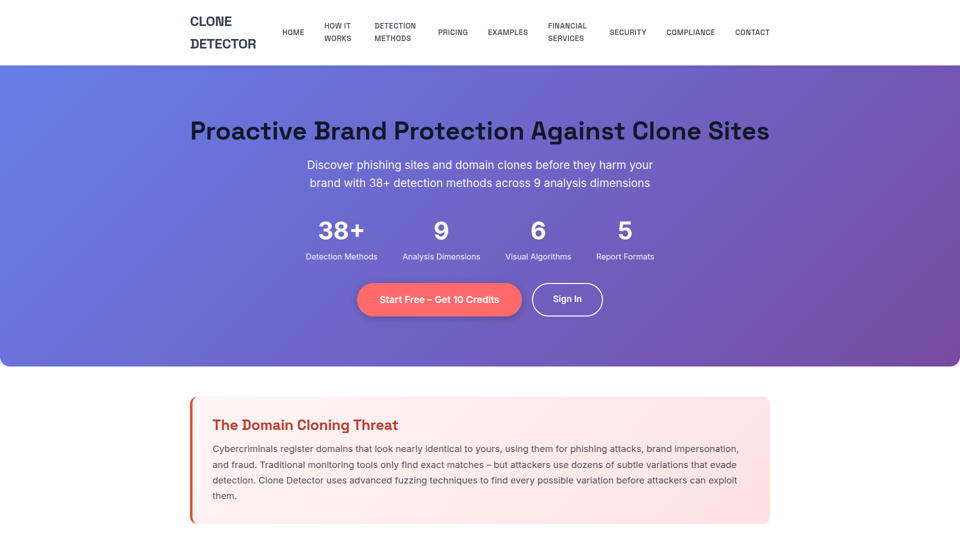
Clone Detector – Brand Protection & Phishing Site Detection Tool
Clone Detector is a brand protection and phishing site detection tool that helps businesses and security teams find fraudulent domain clones and lookalike websites using domain fuzzing, visual similarity analysis, and risk-based reporting. For cybersecurity, compliance, and brand protection roles, it can improve AI-era monitoring by surfacing subtle impersonation threats earlier and supporting faster investigation, reporting, and response.